05 Live Forensics: Discovering Digital Clues in Real Time
In the ever-evolving digital age, crimes are not confined to the physical realm alone. With the widespread use of computers and the internet, law enforcement
Our eDiscovery services are an attorney’s best friend when it comes to litigation. They can help save time and money by efficiently managing the eDiscovery process. With eDiscovery services, you can quickly search through data for court-admissible evidence and uncover hidden secrets that may be relevant to your case. So, if you’re looking to make the eDiscovery process easier and more efficient, our eDiscovery services are the way to go!

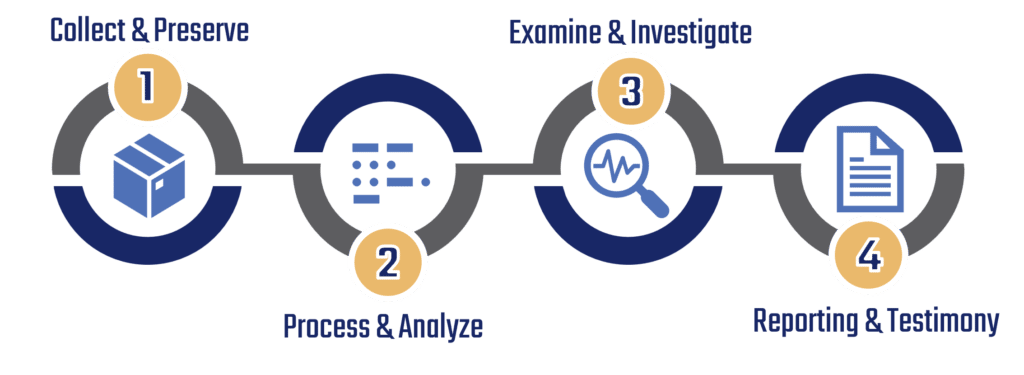
After an initial case review and client meeting, our experts will guide each client through the workflow process and determine which steps are appropriate for each specific case. Though we encourage our clients to utilize all four steps, all steps may not be necessary as our experts will assess client goals and desired outcomes before initiating forensic services.


We can accept / collect data or devices in a variety of ways. After an initial consultation, our team will determine the most cost effective option for your specific needs.


Our workflow process consists of four steps:
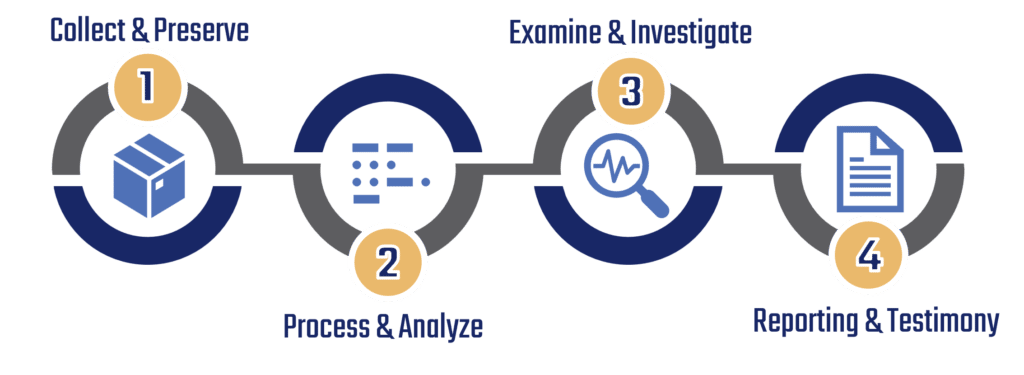
Your case may not require us to utilize each step; a timeline for your case will be determined after an initial assessment by our forensic team. Initial assessments can take up to 24-72 hours.
Our workflow process consists of four steps:
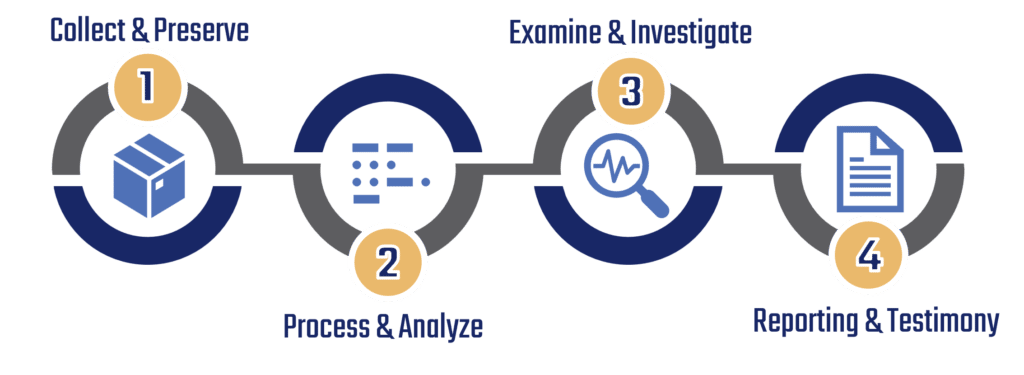
You are welcome to use as many steps as you’d like; or team of experts can also walk you through which steps are most appropriate for your needs.
It is recommended that you unlock and unencrypt any device(s) that are provided to our team of experts. If you do not feel comfortable performing this step, please provide us with the information or credentials we would need to perform this for you.

If you are unable to provide us with credentials to unlock or decrypt your device(s), our experts do have access to advanced tools that can help. Contact us for further details regarding this specialized service.
During our workflow process, device data is stored in a secure location; retention periods for data storage varies on a case-by-case basis.

Once we have completed our workflow, data will either be destroyed or returned based on the contract requirements agreed to.
Our extraction software systems for most of our services includes a reader-friendly conversion tool, typically in PDF format. However, if you need the proprietary data as well, we can assist you by sending a freeware link along with the data file to access the information.
In the ever-evolving digital age, crimes are not confined to the physical realm alone. With the widespread use of computers and the internet, law enforcement
Have you ever wondered how investigators uncover crucial evidence from vehicles to solve crimes, answer unanswered questions in civil cases, or settle insurance claims? Delving
Have you ever wondered how detectives solve mysterious cybercrimes? One powerful tool they use is mobile forensics, which involves investigating smartphones and tablets to uncover
By subscribing you agree with our Privacy Policy and provide consent to receive updates from our company.