DIGITAL FORENSIC SERVICES
Our computer forensic team specializes in investigative techniques to identify, collect, analyze and present digital evidence in a manner that can be used in a court of law or other legal proceedings. We can uncover hidden information stored on computers and other devices, such as cloud accounts, social media, removable media, tablets or even audio/video recorders.

Types of Evidence
Hardware
- Desktops
- Laptops
- Servers
- RAID Storage
- Hard Drives
- Removable Media
- Audio/Video recorders and systems
- Gaming Consoles
Software / Virtual
- Social Media
- Webmail
- Websites
- Cloud Applications, (Slack, WhatsApp, Zoom, Etc.)
- Office 365 Apps
- Cloud Platforms (AWS, Azure, Google, Private, Etc.)
- eFax Services
- Multifunction Copying Services
- Smart Devices Apps (TVs, appliances, IoT, etc.)
Types of Cases
- Legal Holds
- Backup/Archive for Employee Turnover
- Preservation for any HR Investigations
- Confidential/Intellectual Property Theft or mishandling
- Fraud/Embezzlement/Hidden Assets
- Data loss Recovery
- Divorce and Family Matters
- Insurance Claims
- Wrongful Death or Accidents
- Fire/Arson Investigations
- Business Agreement Dispute
- Civil Litigation
- Property Crimes
- Crimes Against Persons
- Criminal Investigations
Types of Clients
- Individuals
- Businesses
- Attorneys
- Law Enforcement
- Prosecutors
- Public Defenders
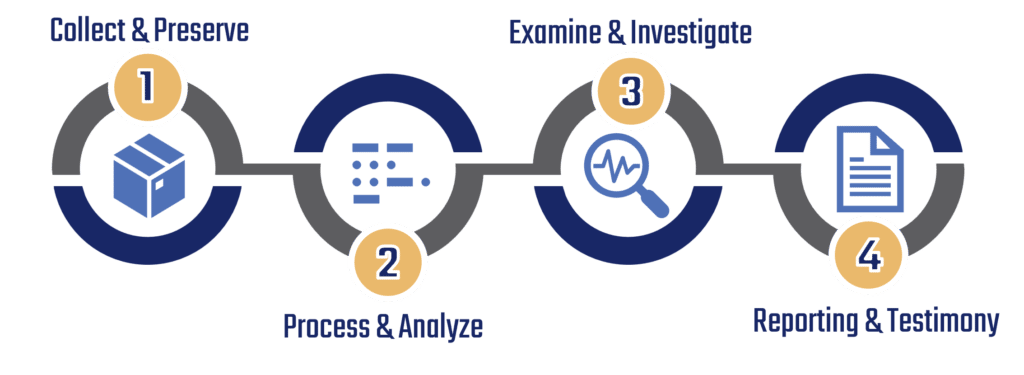
Our Workflow
Tailored to your needs by our team of experts.
After an initial case review and client meeting, our experts will guide each client through the workflow process and determine which steps are appropriate for each specific case. Though we encourage our clients to utilize all four steps, all steps may not be necessary as our experts will assess client goals and desired outcomes before initiating forensic services.
- Establish Scope
- Identify Evidence
- Establish Chain-of-Custody
- Document each process
- Take photographs as appropriate
- Collect device and/or data
- Preserve evidence by making forensic images
- Extract data from devices
- Process all data
- Convert container files, zips, email, spreadsheets, PDFs, and etc. to a readable format
- Index all data for searching capability
- Pre-filter all data for the most relevant data and documents
- Provide early case evaluation to understand the volume of data, user accounts, and any additional information to assist with decision making on next steps

- Review and correlate all evidence
- Identify patterns of forensic interest
- Answer as many investigative questions as possible
- Provide any additional filtering of confidential, privileged, or proprietary information as necessary

- Provide oral or written information to our client
- Prepare written reports, expert reports, affidavits, and/or declarations as requested by client
- Provide presentation overview of findings to client, management, executives, board members, and others as requested by client
- Provide oral depositions and testimony as requested by client
Frequently Asked Questions
We can accept / collect data or devices in a variety of ways. After an initial consultation, our team will determine the most cost effective option for your specific needs.


Our workflow process consists of four steps:
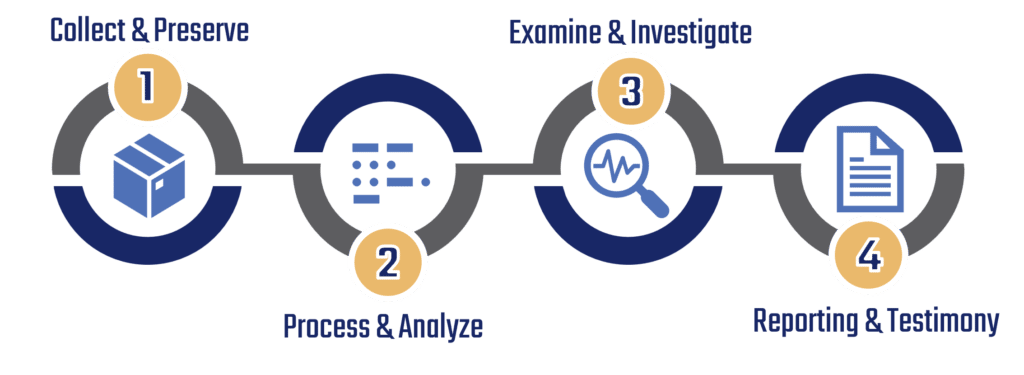
Your case may not require us to utilize each step; a timeline for your case will be determined after an initial assessment by our forensic team. Initial assessments can take up to 24-72 hours.
Our workflow process consists of four steps:
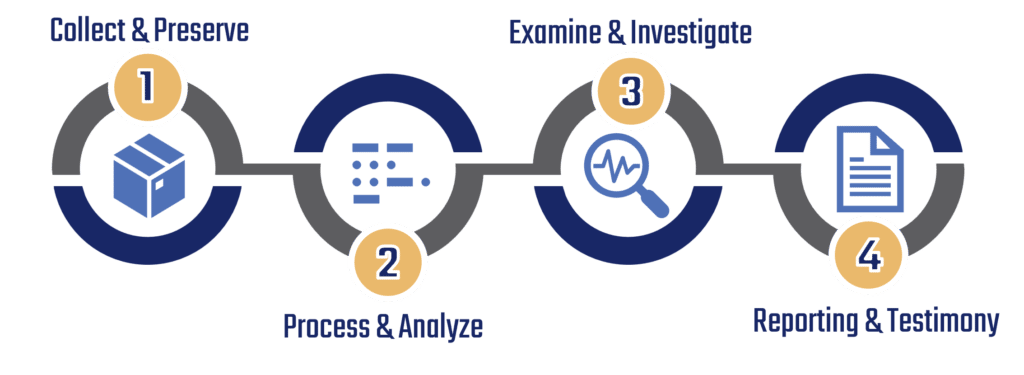
You are welcome to use as many steps as you’d like; or team of experts can also walk you through which steps are most appropriate for your needs.
It is recommended that you unlock and unencrypt any device(s) that are provided to our team of experts. If you do not feel comfortable performing this step, please provide us with the information or credentials we would need to perform this for you.

If you are unable to provide us with credentials to unlock or decrypt your device(s), our experts do have access to advanced tools that can help. Contact us for further details regarding this specialized service.
During our workflow process, device data is stored in a secure location; retention periods for data storage varies on a case-by-case basis.

Once we have completed our workflow, data will either be destroyed or returned based on the contract requirements agreed to.
Our extraction software systems for most of our services includes a reader-friendly conversion tool, typically in PDF format. However, if you need the proprietary data as well, we can assist you by sending a freeware link along with the data file to access the information.
Learn more from our Experts
10 Social Media Forensics: Unveiling the Hidden Truth in Cyberspace
In the digital age, social media platforms have become an integral part of our lives, connecting billions of people across the globe. These platforms enable
09 Cloud Forensics: Unraveling Cybercrimes in the Virtual Realm
The rapid adoption of cloud services has revolutionized the way individuals and organizations store, access, and manage their data. However, this shift towards the cloud
08 Database Forensics: Revealing the Secrets of Data Security
In today’s digital era, databases are critical components of organizations, storing vast amounts of valuable information. However, they are also prime targets for unauthorized access,

